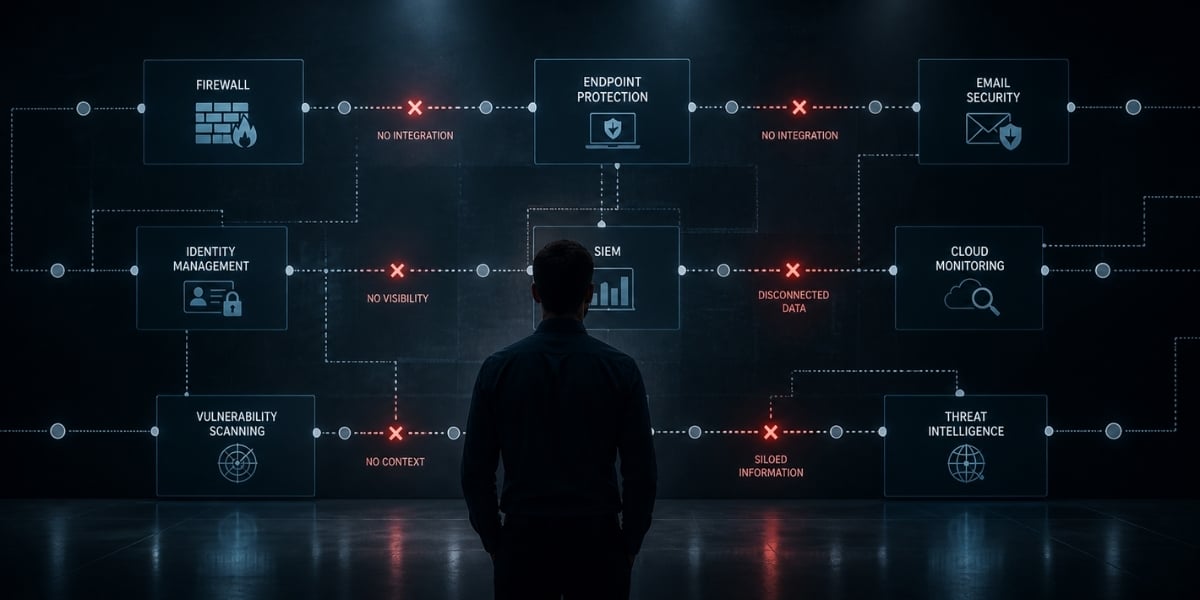
Most security programs look strong on paper. You have a firewall, endpoint protection, email filtering, identity tools, cloud monitoring, and maybe a SIEM pulling logs together. Each tool does its job. Each vendor promises coverage. And yet, breaches still happen. Downtime still hits. Teams still spend hours chasing alerts that lead nowhere.
The reason is simple. Stacking tools is not the same as building a secure environment. When protection gets added one piece at a time, the spaces between those pieces become the real weak spots. Attackers do not break through your strongest control. They slip through the seams where your tools fail to communicate.
This blog breaks down why the layered approach falls short, what a security-first IT model actually looks like, and how a unified design reduces risk far better than piling on more products.
The Hidden Cost of Layered Security
Layered security sounds reasonable. Add more defenses, and you get more protection, right? In practice, it rarely works that way.
Think about how most environments grow. A company buys a firewall. A year later, they add endpoint detection. Then cloud security. Then an identity tool. Each purchase solves a specific problem at a specific moment. But nobody stops to ask how these tools fit together. Nobody maps how alerts flow, how data moves, or how decisions get made when something goes wrong.
The result is a patchwork. You get:
- Blind spots between tools. One product watches the network. Another watches endpoints. A third watches cloud activity. When an attack moves across all three, nobody sees the full picture.
- Redundant spending. Two or three products often do similar work. You pay for overlap without closing real gaps.
- Alert fatigue. Disconnected tools generate thousands of alerts. Staff stop reading them carefully because most turn out to be noise.
- Slower response. When an incident hits, your team has to pull data from five different dashboards just to understand what happened.
These are classic MSP security gaps. Many providers sell security as a list of products rather than a working system. They bolt tools onto existing IT without rethinking how the environment should be built. The client ends up with more licenses and more complexity, but not more actual protection.
What Security-First IT Really Means
A security-first IT approach flips the order of decisions. Instead of building an IT environment and then adding security on top, you design the environment with security already inside every layer.
That means identity, access, infrastructure, cloud, endpoints, and operations all get planned together. Security is not a separate track. It is part of how the system works from day one.
Here is what that looks like in practice:
- Identity is the starting point. Who can access what, when, and from where gets defined before tools are picked. Access rules are written into the architecture, not added later.
- Infrastructure is built for visibility. Logs, telemetry, and monitoring are baked into how servers, networks, and cloud services are set up. You do not have to bolt on a monitoring tool because the ability to see activity is already there.
- Controls reinforce each other. When your endpoint tool spots something unusual, your identity system and network controls react together. One control backs up the next.
- Operations include security from the start. Patching, change management, backups, and recovery planning treat security as a core requirement, not an afterthought.
This is what "integrated by design" actually means. It is a design choice, not a product. And it is the foundation of a real integrated cybersecurity strategy.
Why Alignment Beats More Layers
The old thinking said: more layers mean more protection. The better thinking is: aligned systems mean fewer gaps.
When your tools and processes are aligned, something important happens. Your IT security architecture stops behaving like a collection of parts and starts behaving like one system. That shift changes the outcomes in four clear ways.
1. You See Threats Sooner.
Attackers often use small, quiet steps to move through an environment. A failed login here. A new admin account there. An odd file transfer later. On their own, these events look like noise. Together, they tell a story. Integrated systems connect those dots automatically. Disconnected tools miss them.
2. You Respond Faster.
In a layered setup, response time suffers because the team has to stitch information together during the worst possible moment. In an integrated design, the data is already connected. Your team can act in minutes, not hours.
3. You Spend Smarter.
Integration reveals where you have duplicate tools doing the same job. Consolidation cuts cost without cutting protection. Budget then shifts toward the gaps that actually matter.
4. You Support the Business Better.
Security-first IT is not only about stopping attacks. It is about keeping the business running. When systems are designed together, uptime improves, performance stabilizes, and the team spends less time fixing preventable problems.
This is where real cyber risk reduction comes from. Not from buying another product, but from making sure every part of your environment works with every other part.

How an Integrated Model Gets Built
Moving to an integrated model does not require throwing everything out. It requires a clear plan and the discipline to stick to it. Most organizations benefit from working through these steps:
1. Start with a Full Picture.
Map every tool, process, user, and data flow in your environment. Most teams are surprised by how many tools they own and how little those tools share information.
2. Find the Seams.
Look for the spaces where tools hand off to each other. These are where attackers hide and where response slows down. Write them down. Prioritize closing them.
3. Rebuild around Identity.
Identity is the anchor of a security-first IT model. Clean up access rights. Enforce strong authentication. Remove old accounts. Make sure every login is tied to a real, current user with the right permissions.
4. Standardize Operations.
Patching, backups, configuration, and monitoring should follow the same rules across the whole environment. When operations are consistent, security becomes easier to measure and improve.
5. Test under Real Conditions.
Run drills. Simulate attacks. Watch how your systems, tools, and teams respond. This is where offensive testing, done together with defensive monitoring, reveals what paper plans cannot.
This kind of work is exactly where RedHelm focuses its approach. Our Red Team, Blue Team, and Purple Team operations are built in-house and run as a single, coordinated function. That means offensive testing feeds defensive improvements in real time, and IT operations are shaped by what actually happens under pressure, not by what vendors claim in a brochure. You do not get a handoff between security and IT. You get one model that treats them as the same job.

The Shift From Reactive Defense to Intentional Design
Most security programs are still reactive. Intentional design works differently. You decide how your environment should behave under normal conditions, under stress, and under attack. Then you build toward that.
Organizations that make this shift usually notice three changes within the first year. Incidents are smaller and easier to contain. Recovery is faster because the plan was built in, not improvised. Overall, technology costs become more predictable because fewer surprises trigger emergency spending.
Security-first IT is not a slogan. It is a way of working that treats protection, performance, and business continuity as parts of the same design. When you get that design right, you stop paying for layers that do not line up and start getting real value from every tool, process, and decision in your environment.
The question worth asking is not, “How many layers do we have?” It is, “Do our layers actually work together?” If the honest answer is no, adding another product will not fix it. Rebuilding around a security-first IT model will.
If you want a clearer view of where your layers line up and where they leave gaps, book a conversation with the RedHelm team to walk through what an integrated design could look like for your environment.

May 7, 2026 2:03:27 PM


